Sven Krasser's Blog
Musings on technology, security & sundries
-
Cab Hustle is Now on Itch.io
After releasing my Commodore 64 game project on the Zzap! 64 covermount disk a couple of weeks ago, you can now download the latest version directly from Itch.io (see link below).
-
Cab Hustle is Now Available!
My Commodore 64 game project has now been officially released and is available on the covermount disk of Zzap! 64 Magazine Issue #10. You can get a copy from the magazine’s Patreon page.
-
Backyard Coyote
Since last year, a lot more coyotes have been moving into the neighborhood. Here are a couple of pictures of one that likes to lay out in the sun shining on our backyard hill. Captured with a Nikon Z 6II and Nikkor Z 24-200mm f/4-6.3 VR.
-
Maui
Here are some pictures from a recent trip to Maui. Above the surface cameras: Fuji X100T and iPhone XS; below the surface: GoPro Hero 4 Black.
-
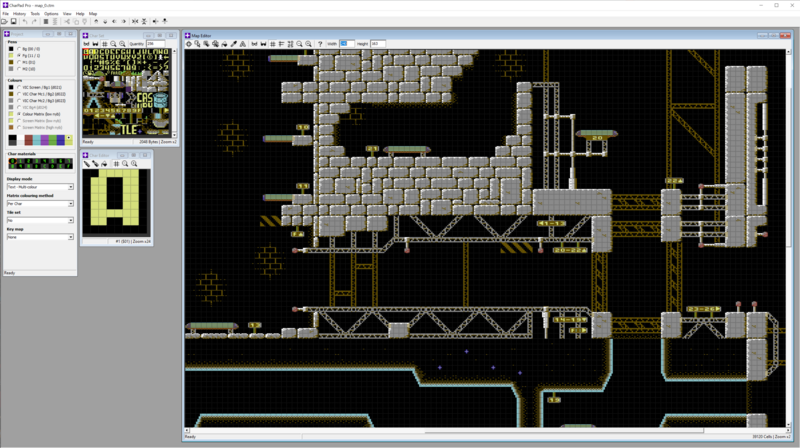
Cab Hustle: The Latest on my C64 Game
Recently I found a tad more time to work on my C64 game, Cab Hustle. There is also a new video on my YouTube channel showing some of the changes (you can watch it at the bottom of this post). Let’s take a look at where things stand and what is new since my last post about the game.
-
Recent Writing on AI in Cybersecurity
There are a couple of new articles I penned in recent months on Artificial Intelligence and Machine Learning in cybersecurity:
- How Human Intelligence is Supercharging CrowdStrike’s Artificial Intelligence – CrowdStrike Blog
- Why AI is now Table-Stakes in Cybersecurity – Digitalisation World
And in case you’re also a German speaker:
-
Arduino-Powered Pants
While my next sewing project has seen little progress (I’ve been working on a knit t-shirt, but the stretchy fabric is killing me), my wife just published a new post on her blog about her adventures sewing, wiring, and programming space pants with Arduino-driven twinkling stars, i.e. LEDs.

-
Around Mammoth with the TTArtisan 11mm F2.8 Fisheye Lens
The most recent family trip was to go skiing in Mammoth, CA, and I brought my latest lens with me, the TTArtisan 11mm F2.8 Fisheye. It’s my second third-party lens for the Nikon Z system. Like my Tokina SZX 400mm f/8, the TTArtisan is a manual focus non-CPU lens. But those commonalities aside, it is the polar opposite of the Tokina. It has a fast f/2.8 maximum aperture (exclusively controlled over an aperture ring since the lens does not exchange any data with the camera) in contrast to the slow fixed f/8 aperture of the Tokina. And with a focal length of 11mm it is squarely in the ultrawide angle territory, compared to the Tokina with its 400mm super-telephoto focal length at the other end of the spectrum. It ships in a nicely designed box, and considering its compact dimensions it brings some weight to the table: 439g according to the manufacturer.

-
Recent Progress on “Cab Hustle”
Since my last post in October about Cab Hustle, my Commodore 64 retro game programming project, there has been some progress—mostly under the hood. Before diving into it, the game was also covered on the Universe64 YouTube channel. That was a bit of a pleasant surprise since outside of this blog and on my YouTube channel, I haven’t been talking about it at all.
As a quick review to catch everyone up: Cab Hustle is a two-dimensional thrust/gravity-based game. The objective is to pick up passengers by landing on platforms and then bring them to their requested destination platform. Here’s what’s new (alongside some background about developing for the C64).

